Install OpenStack on KVM – How To Configure KVM for OpenStack

Typical OpenStack cloud setup consists of more than one node (usually one Controller node and several Compute nodes), which requires lot of physical computers / servers available to perform the installation. This complicates the situation, especially if we need to test OpenStack on many nodes. Fortunately we can use Linux KVM (Kernel-based Virtual Machine) to create OpenStack on virtual nodes and avoid problems with obtaining physical hardware.
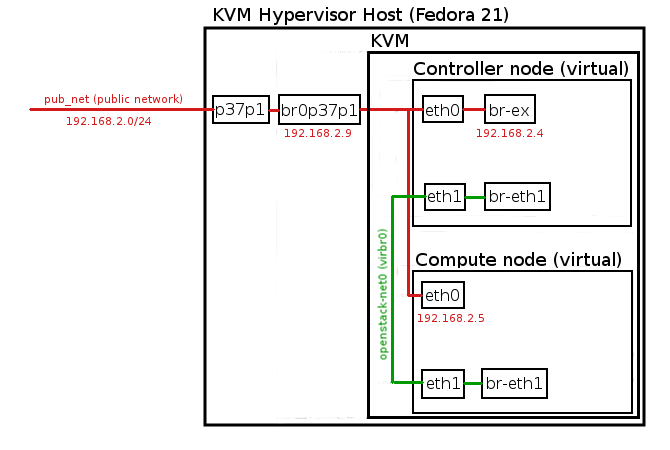
In this tutorial we will show you how to install OpenStack on KVM on Fedora 21 based hypervisor. We will run Openstack installation on two KVM based virtual nodes (Controller and Compute).
The most important part in configuring KVM for OpenStack installation is network setup, we also need to secure some resources (VCPUs, RAM, disk space) on KVM Hypervisor to create two virtual nodes.